Mobile devices have become essential tools in modern organizations, enabling employees to work from virtually anywhere. However, the rapid expansion of smartphones, tablets, and laptops in the workplace has introduced serious security, compliance, and management challenges. Companies must protect sensitive data while maintaining productivity and user satisfaction. Mobile Device Management (MDM) tools such as Microsoft Intune play a critical role in meeting these demands by offering centralized control, policy enforcement, and comprehensive security capabilities.
TLDR: Mobile Device Management tools like Microsoft Intune allow organizations to centrally manage, secure, and monitor mobile devices used for work. They provide features such as device enrollment, policy enforcement, app management, and data protection. These tools are essential for supporting remote and hybrid work environments while reducing security risks. Implementing a robust MDM strategy strengthens compliance and operational efficiency.
Table of Contents
The Growing Need for Mobile Device Management
The modern workforce is increasingly mobile. Employees use corporate-issued devices, personal smartphones under Bring Your Own Device (BYOD) policies, and remote work setups that extend beyond traditional office networks. Without structured management, this diversity of endpoints can expose organizations to significant risks, including data breaches, regulatory violations, and operational disruptions.
Key challenges organizations face include:
- Data leakage from lost or stolen devices
- Unauthorized access to corporate applications
- Unpatched operating systems vulnerable to cyberattacks
- Lack of visibility into device health and compliance
- Difficulty enforcing consistent policies across platforms
MDM platforms such as Microsoft Intune provide centralized oversight and automated controls to address these issues effectively.
[h2>The Core Capabilities of Microsoft Intune and Similar MDM Tools
Microsoft Intune, part of the Microsoft Endpoint Manager ecosystem, is a cloud-based service that focuses on mobile device management and mobile application management (MAM). Its capabilities extend across iOS, Android, Windows, and macOS devices.

Core features typically include:
- Device Enrollment: Simplifies onboarding by automatically registering company or personal devices into the management platform.
- Policy Enforcement: Configures security settings such as password requirements, encryption mandates, and access controls.
- Application Management: Controls which applications can be installed and manages updates.
- Compliance Monitoring: Continuously evaluates devices against predefined security standards.
- Remote Actions: Enables remote wipe, lock, or reset capabilities if a device is compromised or lost.
These capabilities ensure that every managed device aligns with organizational security policies while minimizing manual administrative effort.
Strengthening Security Through Centralized Control
One of the most significant advantages of MDM tools is their ability to centralize control over diverse device ecosystems. Rather than relying on individual users to maintain security standards, administrators define and enforce policies across the entire organization.
For example, Microsoft Intune allows administrators to:
- Require multi-factor authentication for access to corporate email
- Enforce full-device encryption to protect stored data
- Block devices that do not meet operating system version requirements
- Restrict copying data from corporate apps to personal apps
This level of standardized enforcement reduces reliance on user behavior and significantly lowers the risk of human error, which is a leading cause of data breaches.
Supporting BYOD Without Sacrificing Security
Bring Your Own Device policies are attractive for cost savings and employee flexibility. However, allowing personal devices to access corporate networks raises legitimate concerns about privacy and security. MDM tools like Intune address this tension by implementing containerization and application-level management.
Instead of controlling the entire device, administrators can manage only the corporate applications and data within a secure container. This approach:
- Protects corporate information
- Preserves employee privacy
- Separates work and personal data
- Allows selective data wipe without affecting personal files
Such balanced controls encourage user adoption while maintaining enterprise-grade protection.
Enhancing Compliance and Regulatory Readiness
Regulatory frameworks such as GDPR, HIPAA, and ISO standards impose strict requirements on data protection and device security. Failure to comply can result in substantial penalties and reputational damage.
MDM platforms assist compliance efforts by:
- Generating detailed audit logs
- Providing compliance dashboards
- Automating policy enforcement
- Restricting access to non-compliant devices
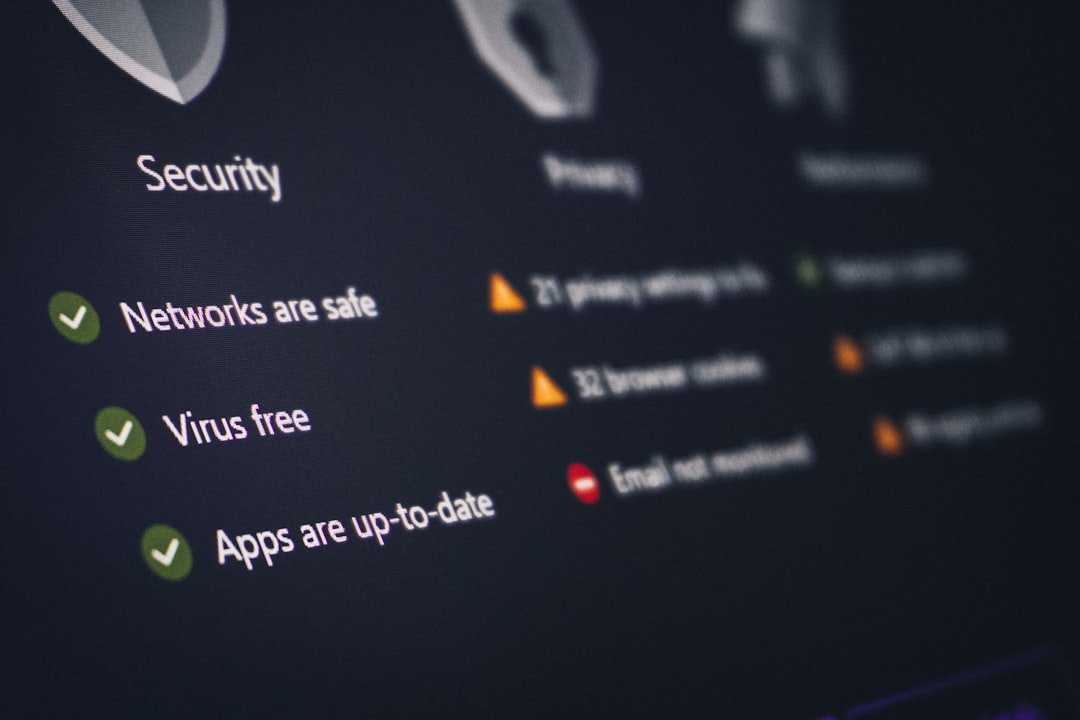
By maintaining continuous oversight and producing verifiable records, organizations demonstrate due diligence and improve their regulatory posture. Microsoft Intune integrates particularly well with identity management solutions, enabling conditional access policies that grant or deny access based on real-time device compliance status.
Streamlining IT Operations and Reducing Overhead
Manual device management is both time-consuming and prone to inconsistency. MDM tools reduce operational complexity by automating repetitive tasks and offering centralized monitoring dashboards.
Operational benefits include:
- Zero-touch provisioning: New devices can be configured automatically before reaching employees.
- Automated updates: Security patches and application updates can be deployed remotely.
- Bulk configuration changes: Policy updates apply to thousands of devices simultaneously.
- Real-time monitoring: IT teams can quickly identify and isolate compromised endpoints.
This efficiency allows IT departments to focus on strategic initiatives rather than routine maintenance tasks.
Integration With Broader Security Ecosystems
Another strength of solutions like Microsoft Intune is their integration capabilities. Intune works seamlessly with Azure Active Directory, Microsoft Defender, and other enterprise security services. This interconnected ecosystem enhances threat detection and response.
For example, if a device is flagged for suspicious activity by a security monitoring system, a conditional access policy can immediately restrict that device’s access to sensitive resources. This coordinated response minimizes potential damage and accelerates remediation.
When integrated into a broader Zero Trust architecture, MDM becomes a foundational component. Every device must be verified, compliant, and authenticated before accessing corporate assets. This dynamic security model is increasingly essential in distributed work environments.
Real-World Use Cases Across Industries
Organizations across industries use MDM tools to address specific operational needs:
- Healthcare: Protect patient records on tablets and smartphones used by medical staff.
- Finance: Enforce encryption and secure authentication on devices handling confidential financial data.
- Education: Manage student and faculty devices with standardized policies.
- Retail: Secure point-of-sale tablets and inventory management systems.
In each scenario, centralized management reduces risk while enabling mobility and productivity. The adaptability of platforms like Microsoft Intune makes them suitable for organizations of various sizes and complexity levels.
Challenges and Considerations Before Implementation
Although MDM platforms provide substantial benefits, successful implementation requires careful planning. Organizations must evaluate:
- Device diversity: The range of operating systems and hardware models in use
- User training: Ensuring employees understand enrollment processes and security requirements
- Privacy concerns: Particularly under BYOD programs
- Policy development: Defining clear and enforceable standards
A poorly defined rollout strategy can create user resistance or operational disruptions. Clear communication and phased deployment help mitigate these risks.
The Future of Mobile Device Management
As cyber threats grow more sophisticated, MDM tools continue to evolve. Artificial intelligence-driven threat detection, automated remediation workflows, and deeper integration with cloud services are shaping the next generation of device management.
Future advancements are expected to focus on:
- Predictive risk scoring based on device behavior patterns
- Enhanced user identity verification methods
- Unified endpoint management that consolidates desktops, servers, and mobile devices into a single framework
- Greater automation in responding to compliance breaches
Microsoft Intune is already moving toward unified endpoint management, reflecting the broader industry shift toward comprehensive digital workspace security.
Conclusion
Mobile Device Management tools like Microsoft Intune have become indispensable in today’s enterprise landscape. They provide centralized oversight, enforce consistent security policies, support regulatory compliance, and streamline IT operations. As organizations continue to embrace remote work and BYOD models, the importance of structured device management will only increase.
A carefully implemented MDM strategy does more than protect data—it strengthens resilience, maintains trust, and supports sustainable growth in a highly connected world. For organizations seeking to balance flexibility with security, investing in a robust mobile device management solution is not optional; it is a strategic necessity.
